SecureTower DLP Features & USP
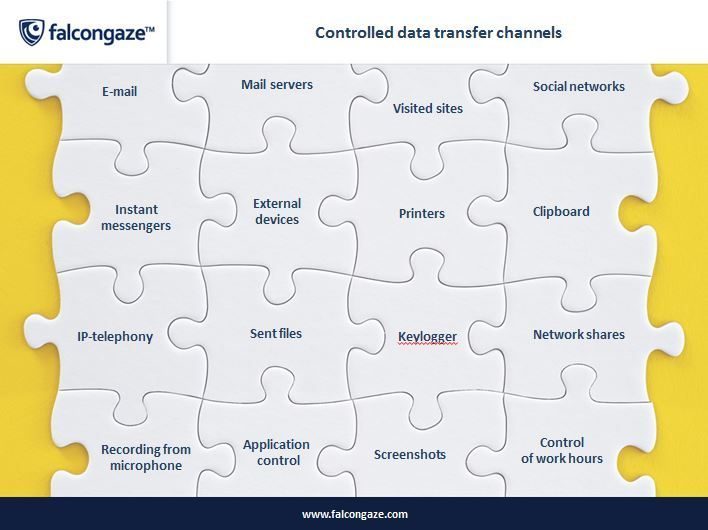
- Control of Data Transfer Channels
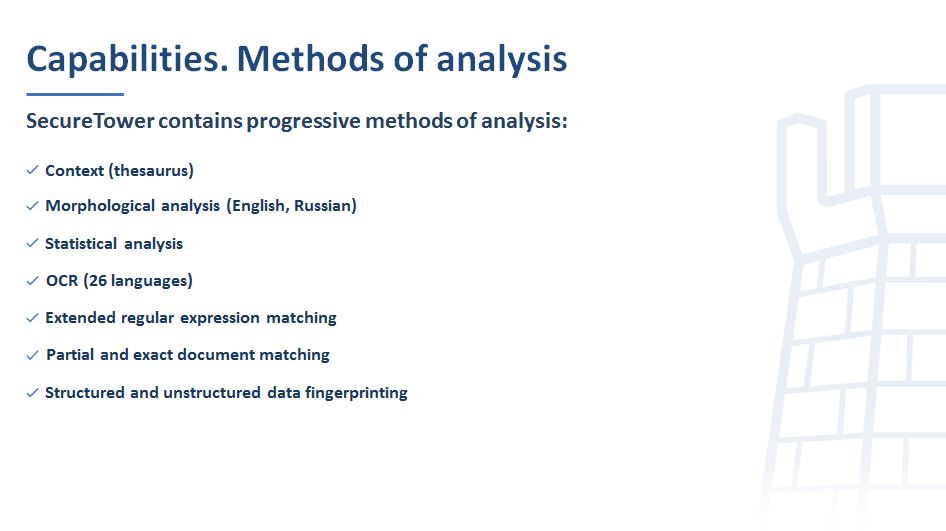
- Detection of Sensitive Data Content
- Data Leak Prevention
- Incident Response
- Employee Monitoring
- Archive of Intercepted Data
- Reports Based on Gathered Information
E-mail
SecureTower provides control of all messages of most popular mailbox servers, according to POP3, SMTP and IMAP protocols, as well as capture and lock-up of messages using MAPI protocol.
The system checks the compliance with the security policies for messages, sent by means of Microsoft Exchange Server, Lotus Notes, Postfix, Sendmai, etc. Besides, the system supports capture of messages from external mail services in free mail services, such as Gmail, mail.com or any other mail service.
Messengers
Employees of modern companies prefer to carry out business communication, using messengers and social networks, rather than by e-mail, with increasing frequency. To control these channels, the option of message and transferred file capture for practically all popular messengers is implemented in SecureTower. The DLP system can control instant messaging protocols OSCAR (ICQ/AIM), MMP (Mail.Ru Agent), XMPP (Jabber) (Miranda, Google Talk, QIP Infium, PSI), YIM (Yahoo! Messenger), SIP, as well as capture text and voice messages and files in Skype, Viber, MS Lync and Telegram.
Social networks
Apart from messengers, employees more and more frequently use social networks such as Insagram, Facebook, twitter etc., for business communication. The DLP system controls communication of the staff in blogs, online chats, forums, etc.
Web activity
SecureTower allows to build a complete picture of the employee web activity throughout th
e working day. The DLP system helps to get information about the websites, visited by the employee, the time, spent on these websites or any messages sent.
Cloud storage
Employees can use cloud storages as part of the working process, but security incidents are also possible. SecureTower tracks all files, downloaded by the user into the Internet through a browser, besides, file capture in desktop applications for such cloud services as Dropbox, OneDrive and Yandex.Drive is also possible.
Applications
The DLP system tracks the applications, used by the employees throughout the working day. On the basis of the results, obtained by this option, you can check what applications were used by the employee more frequently and what period of time was devoted to the labour activities. Besides, the system can lock up particular applications, determined by the administrator.
Personnel control
One of the main factors, pre-determining choice of the DLP system, is a possibility to control the staff activities. In view of this, an option of working time control which allows to see the actual time spent on fulfillment of any task by the employee is implemented in SecureTower.
Moreover, you can get the broad picture of the employee’s working day by means of the keylogger, audio and video monitoring and desktop screenshots.
Workstation control
SecureTower provides control and prevention of file transfer to external media. The system performs automatic scanning of the documents, sent for printing or USB drive, for confidential information, and in case of detection of this information, notifies the administrator and allows to take preventive measures to remediate the incident.
Besides, SecureTower tracks connection and disconnection of devices from the workstations, controls information copying and carries out the computer access audit.
Workstation indexing
To ensure checks for presence or absence of confidential documents on the workstation, SecureTower is provided with quick search on all computers in the local network, which includes the manual mode. The search is possible both by names and file attributes.
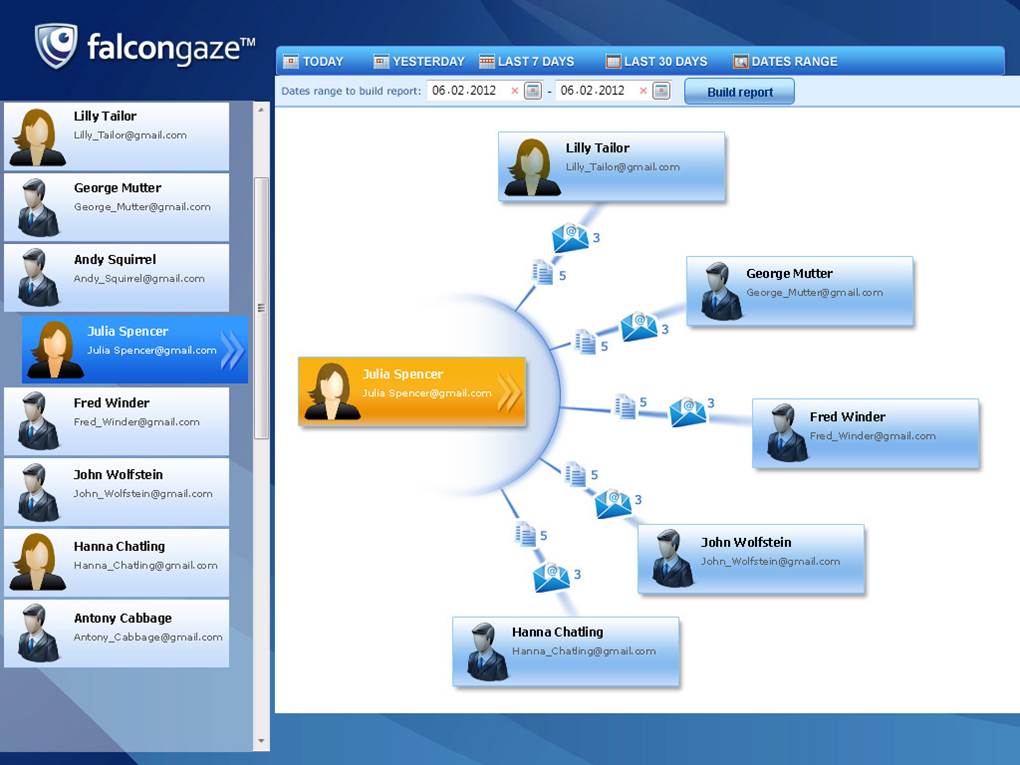
Personnel interactions
To detect the personnel interactions, SecureTower uses a graph analyzer, in which profiles, automatically linked to ActiveDirectory, are created for every employee, and displays the employee’s communication with other people. This profile shows the employee e-mail addresses, names in messengers, accounts in social networks an on other websites.
To detect outside ill-wishers, SecureTower registers the addresses of the external abonents and also creates profiles for them. It ensures quick detection of an external intruder or, for example, a recruiter, working for a competitor company.
Reports
Completely settable reports on security incidents and daily activities of the staff are available for security department employees and managers of structural units. You can also set up automatically scheduled reporting and report sending to e-mails.
SecureTower Capabilities
SecureTower Screenshots