Understanding Ransomware: Protecting Your Data in the Digital Age
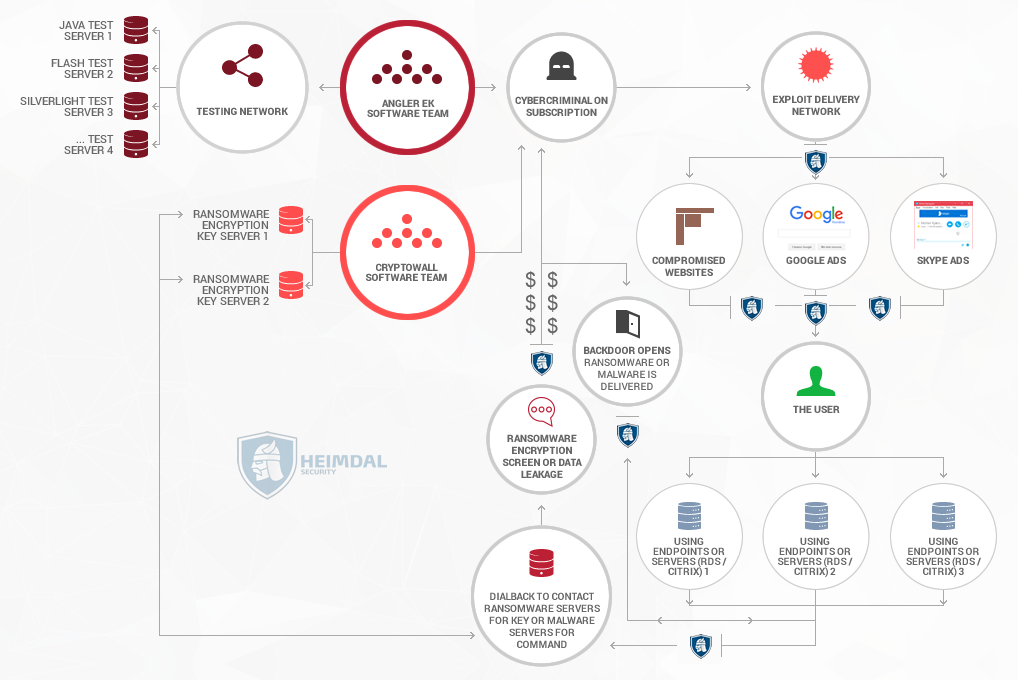
What is Ransomware? Ransomware is a type of malicious software (malware) designed to block access to a computer system or data until a ransom is paid. This form of cyber extortion has gained significant notoriety due to its devastating impacts on individuals and organizations alike. When ransomware infiltrates a system, it typically encrypts the files, […]